Proof of Continuity becomes easier with an Edge
I’m beginning to believe identity is structurally broken for the age of AI agents. We are rapidly moving from a world where human users interact directly with applications to a multi-hop ecosystem where autonomous agents orchestrate complex tasks on our behalf. Yet, the foundational identity protocols we use to secure these interactions haven’t fundamentally changed.
The Trap of Proof of Possession Today, authorization is heavily dominated by Proof of Possession (PoP). Whether it’s an OAuth token, a JWT, or a traditional API key, the logic is the same: authority derives entirely from holding the artifact. This works reasonably well for a single hop (User ? Service). But it fails catastrophically across chains (User ? Agent ? Service A ? Service B).
At each hop, the system simply asks, “Do you possess a valid token?” It doesn’t enforce causal continuity. This is the root of the Confused Deputy problem. If a privileged AI agent is compromised via prompt injection, it can exploit its ambient authority to execute attacks that were never intended by the original user. PoP verifies artifacts, not the continuity of the relationship.
Enter the PIC Protocol Solving this requires a shift in how we model trust. Instead of asking “what do you possess?”, we must ask “can you prove you can continue this chain?”
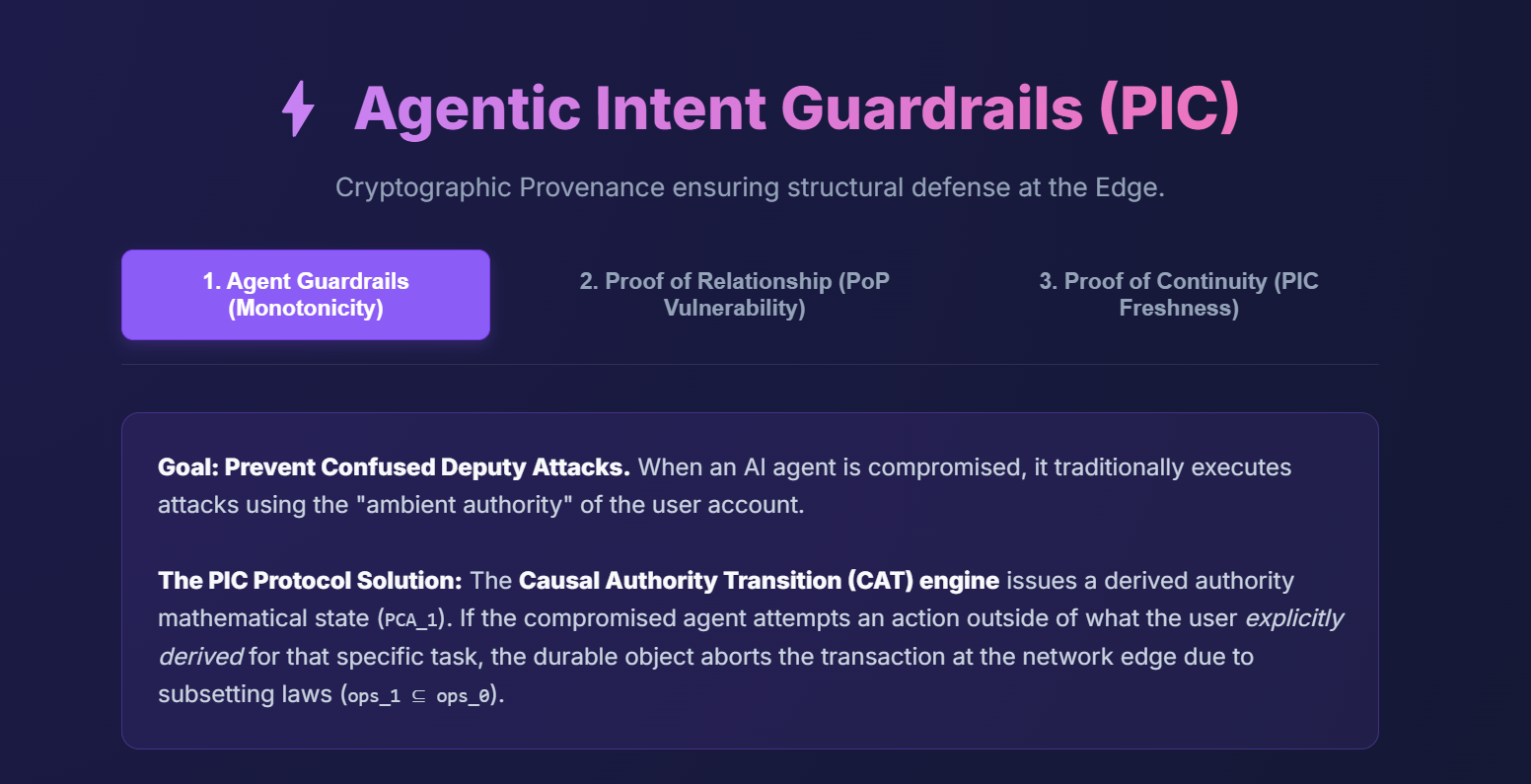
This is the core premise of the Provenance Identity Continuity (PIC) model. PIC enforces three invariants at every execution hop:
- Provenance: The causal chain is traceable and unbroken from origin to end.
- Identity: The origin identity is immutable and acts as the singular source of authority.
- Continuity: Authority can only decrease (monotonicity). An agent cannot expand its permissions beyond what was explicitly delegated for a specific task.
Under PIC, the Confused Deputy attack isn’t just mitigated—it becomes mathematically inexpressible.
Building the Trust Plane at the Edge In my own recent explorations building pico-SaaS applications entirely on serverless architectures, the need for a globally distributed, low-latency trust plane became obvious. You cannot route every multi-hop agent interaction back to a centralized database to verify continuity.
The edge is the natural home for this. Cloudflare Workers and Durable Objects provide the exact primitive needed to build a Causal Authority Transition (CAT) engine. By decentralizing state, we can evaluate Proof of Continuity (PoC) challenges within milliseconds of the executor, keeping latency low without sacrificing security.
The Simulation To make this tangible, I built an interactive architecture demo of the PIC protocol running on the Cloudflare edge.
You can run the active simulation here: Indra PIC Protocol – Architecture Demo
The demo walks through three critical scenarios:
- Agent Guardrails (Monotonicity): Watch the CAT engine dynamically enforce subsetting laws, terminating structural attacks at the edge when a compromised agent attempts an action outside its derived authority.
- Proof of Relationship: See firsthand how legacy Bearer Tokens inherently lack network relationship modeling, allowing stolen cache tokens to be replayed blindly.
- Proof of Continuity: Experience how PIC mathematically binds Causal Authority to hardware enclave keys, causing replay attacks from unauthorized devices to fail the PIC Causal Challenge (PCC).
Looking Forward I’ve been publishing thoughts on the web’s evolution for over 30 years, and the shift from “Proof of Possession” to “Proof of Continuity” feels like one of the most critical infrastructure upgrades we are facing today. As we hand over more autonomy to agents, we must ensure our trust models are built to constrain them. The network edge is exactly where those constraints need to live.